Build and Operate Your CMMC-Ready Environment
Input Trace designs, deploys, and operates secure enclaves for Defense Industrial Base manufacturers, and prepares you for formal C3PAO assessments



THE PROBLEM.
Your company handles Controlled Unclassified Information (CUI) and needs a CMMC Level 2 Certification
Now you're asking:
How can I efficiently become CMMC-ready?
You need a turnkey, CMMC-ready environment that’s already architected, deployed, and operated by people who live and breathe these requirements. That’s Input Trace.
How can we achieve this without internal IT staff?
We can help by building the cloud environment, implementing controls, running logging and monitoring, generating evidence, and keeping you compliant month after month, so you don't have to become a cybersecurity company just to cut parts for the DoD.
When it’s time for your assessment, hand them your shared responsibility matrix, and we handle the rest. We take your business requirements and build a tailored cloud enclave around them. That enclave clearly segments responsibility, pushing many of the technical controls into the environment we design and operate for you.
The Path to Success
Input Trace starts every engagement by assessing your organization's CMMC maturity. Before we architect anything, we need to understand where you are against CMMC Level 2 requirements. This maturity baseline drives everything.
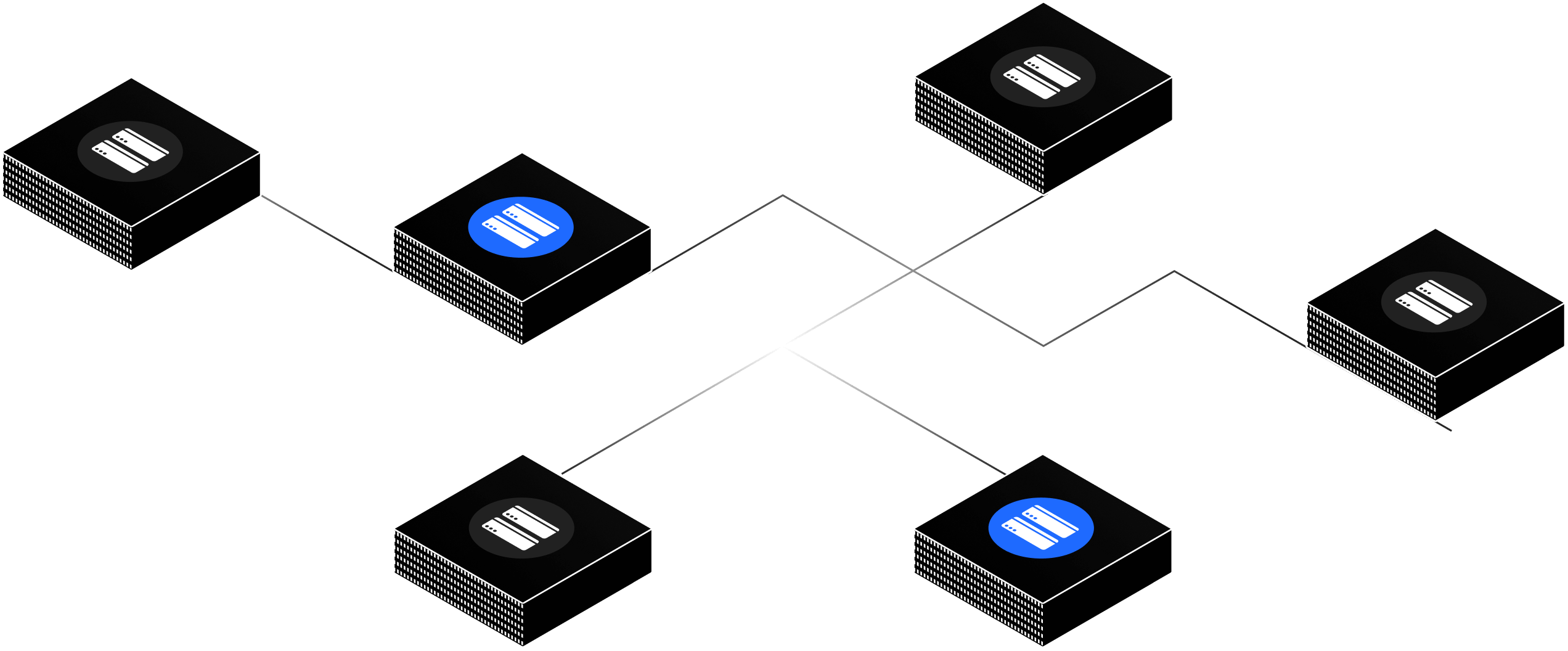
CMMC maturity isn't just a score, it's a roadmap that tells us exactly what technical changes your environment needs. We architect and deploy the Azure infrastructure required to close those gaps: secure enclaves with proper network segmentation, identity controls, hardened endpoints, and logging pipelines designed to generate evidence continuously.
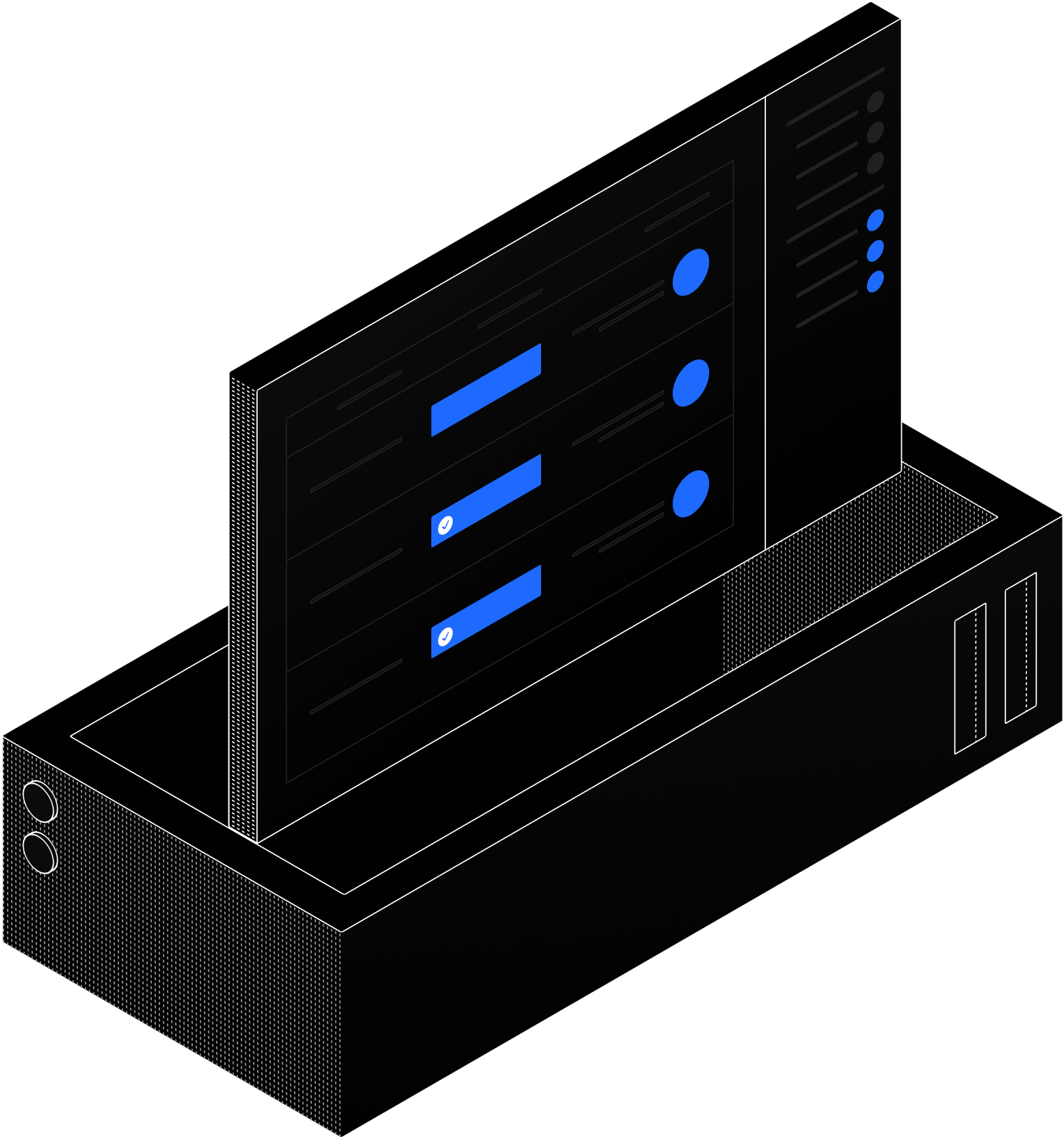
Once deployed, we operate the environment on your behalf—identity management, vulnerability scanning, patch orchestration, and monthly evidence generation, ensuring your CMMC maturity doesn't regress.
When you're ready for formal C3PAO assessment, we validate your artifacts, verify control implementation across all Assessment Objectives, and prepare your team for the review process.
The goal is CMMC certification. The path is technical maturity backed by real infrastructure.
Path to Success
Real Architecture. Real Evidence. Real CMMC
We're building a library of technical resources that show how CMMC-ready environments are architected. Network diagrams, Terraform examples, Sentinel configurations, and real evidence artifacts mapped to Assessment Objectives.